The Information Security Provider
atsec IT Security Blog
News about Common Criteria, FIPS, Conferences
and other topics revolving around IT security.
For a non-paginated list of all of our blog posts, head over to our Blog Archive page.
-

atsec at the (virtual) International Common Criteria Conference (ICCC) 2020
atsec participated in ICCC 2020 from November 16th through 18th, which for the first time had to be held fully virtualized due to the worldwide pandemic. The ICCC used the same conference platform as for the ICMC 2020. In addition to attending the ICCC 2020, a number of…
-

You Raise Me Up – ICMC 2020
It has become an atsec tradition to produce an animation with an FIPS-relevant topic for the ICMC. This year it has the transition from FIPS 140-2 to FIPS 140-3 as the subject – with a personal touch. Yi Mao presented the animation during her opening speech at the…
-
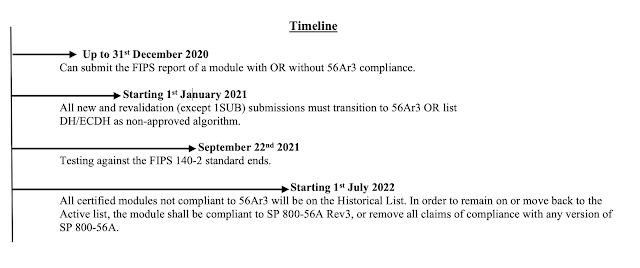
Transitioning to NIST SP 800-56A Rev3: what you need to know
by Swapneela Unkule NIST SP 800-56A provides recommendations for Pair-Wise Key-Establishment Schemes Using Discrete Logarithm Cryptography. Diffie-Hellman (DH), Elliptic Curve DH (ECDH) and Menezes-Qu-Vanstone (MQV) key-agreement schemes are specified in this standard. These Key-Agreement Schemes (KAS) are widely used in network protocols such as TLS. The SP 800-56A…
-

atsec’s 20 Year Anniversary
It was the beginning of January when I first heard about the new virus causing severe flu-like symptoms, such as upper respiratory infection, spreading throughout China. I started to worry about our China team. Nevertheless, we continued to plan for the global celebration of atsec’s 20th anniversary, assuming…
-

atsec leading in Automated Cryptographic Validation Testing
With the sunset of the Cryptographic Algorithm Validation System (CAVS) at end of June 2020, algorithm testing for NIST and NIAP validations and evaluations must now be performed using the Automated Cryptographic Validation Testing System (ACVTS). The list of issued CAVP certificates using ACVTS (i.e. the certificates prefixed…
-
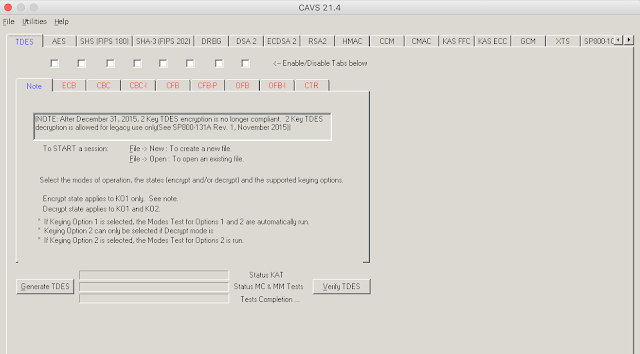
Bye bye, CAVS tool, old friend…
Dear CAVS Tool, We want to congratulate you on years and years of dedicated service. Without you, algorithm testing would not have been what it is today, and we salute you for staying with us for so long. On June 30th you will finally get your well-deserved retirement.…
-
Congratulations to Qualcomm
One of the rewards of working in the evaluation and testing business is to see our customers succeed and show the results of their efforts. We are always happy to work with organizations who are committed to IT security and want to improve their products and processes for…